The Two Failures Every Guardhouse Knows
A resident hosts a wedding reception, milestone birthday, or large festive open house. Guests arrive across the evening. Some early, some late, some in convoy. The guardhouse faces two bad options that look different on the surface but produce the same outcome.
The first is to type every guest’s name, IC number, and unit destination one by one. By the third car, the queue has spilled past the barrier gate. By the tenth, the host is calling security to ask why nobody is being let in. By the twentieth, the guard has stopped registering altogether and started waving cars through with a clipboard nod. The security record dies quietly somewhere between car five and car ten.
The second is more common than most management offices admit. The resident sends the guardhouse a list of car plate numbers in advance, usually through WhatsApp. The guard prints it, sticks it on the wall, and triggers the barrier manually whenever a listed plate arrives. No name. No IC. No system record at all. If something goes wrong that evening, the development has nothing to investigate with the next morning.
Both routes hand the same outcome to the JMB. A weekend that should have been a community celebration becomes a security gap that nobody can audit.
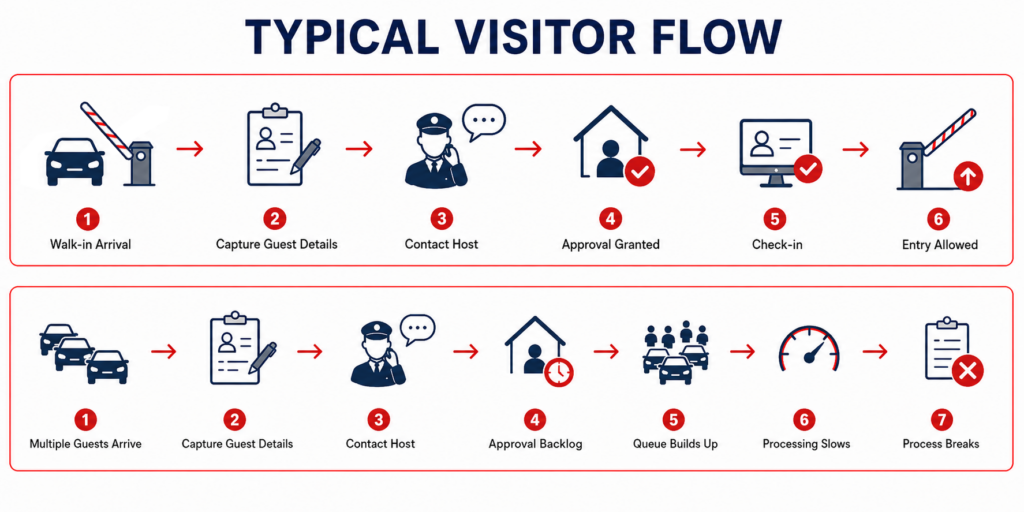
Why Single-Visitor Workflows Break at Group Scale
Most visitor systems are built around the one-guest-at-a-time pattern. Walk-in registration, host call, approval, check-in. That model holds up for daily guests but collapses the moment a single unit invites dozens of visitors to the same event. The bottleneck is not the guard’s typing speed. It is the assumption built into the workflow that every visitor is unrelated to every other.
A group of forty guests heading to the same penthouse for the same wedding is not forty independent visit events. It is one visit with forty members. A system that cannot recognize that distinction can never move faster than a guard’s hands.
Pre-Registration Is the Only Way Out
The host already knows the guest list before the event. The guardhouse should never be the original source of that information.
A shareable invitation link from the resident pushes data entry to guests, allowing them to submit their name, IC, and vehicle plate on their own phones before they even leave home. By the time the first car arrives, the system already recognizes them. The guard is no longer a typist. The guard becomes a verifier, which is what the role was supposed to be in the first place.
This shifts the gate dynamic. The bottleneck is not removed by hiring more guards or buying faster tablets. It is removed by moving the data entry off the gate entirely.
What Group Invitation Architecture Actually Requires
Three layers must work together for this to function in practice. Resident-side invitation generation. Guest-side self-registration. Guard-side group consolidation.
iNeighbour handles the first through its Visitor Management module. Residents create one invitation with multi-day validity covering rehearsal day, prep, and the actual event, generate a shareable link, and send it through whatever channel they already use to coordinate with their guests. Each guest opens the link and completes their own pre-registration with the required details.
When guests start arriving across the evening, iVizit, the guardhouse tablet app, consolidates the entire group under a single visitation record. The guard sees one event, not dozens of disconnected entries scattered across the day’s logs. The management office, opening the report the next morning, sees the same view: one consolidated visit with all members listed underneath, not a fragmented log that requires manual reconstruction to understand what actually happened.
Group Visits Should Not Bypass Security
Speed cannot come at the cost of the security record. Every guest who pre-registers still creates a visitor profile. Every profile is still checked against the development’s blocklist by IC number and vehicle plate before access is granted. Every check-in still appears on the Live Activity monitor with overstay tracking enabled. Every action remains in the audit trail the next morning.
This is the operational difference that matters. As we explored in The Visitor Profile Is the Security Layer, a visitor logbook only records events. A visitor profile records people. Group invitations should accelerate the first without weakening the second.
The host gets convenience. The committee still gets the audit trail. The guard stops being a data entry counter and goes back to verifying who is actually arriving.
Why This Is Not Only About Parties
Weddings and birthdays make the case obvious, but the same architecture solves several other recurring problems JMBs already face.
AGMs require controlled access for unit owners. Non-owners attending is a governance risk that voting outcomes can later be challenged on. Renovation crews and cleaning teams arrive in groups across multiple days with shifting members each shift. Festive open houses during Hari Raya, Deepavali, and Chinese New Year multiply visitor volume across the entire development at once, not just one unit.
Each scenario shares the same architectural requirement. Pre-registration moves data entry away from the gate. Group consolidation gives the management office one record to read instead of forty. Visitor profile checks remain non-negotiable.
A guardhouse that records 100 names is a logbook. A system that pre-registers them, profiles them, and consolidates them as one event is a security layer.
