Why a Logbook Cannot See What Is Coming Back
Every JMB/MC/RA committee has a story. The food delivery rider who entered the wrong block twice in one week, both times waved through because his face looked familiar to a different guard. The contractor who arrived claiming to be a previous tenant collecting forgotten items, presenting an access card the system had never deactivated. The unfamiliar face who appeared three evenings in a row at the visitor lobby before someone in management asked the question nobody else had thought to ask: who is this person, and which unit is he actually visiting?
In each case, the visitor was recorded. In each case, the logbook was complete. In each case, nothing was prevented.
This is the problem that residential security has been quietly carrying for years. The visitor logbook, whether kept on paper or on a screen at the guardhouse, captures the present moment and forgets it the next day. It does not remember. It does not connect. It does not warn. And yet committees and residents trust it as if it does.
The gap between recording a visit and protecting a community is wider than most committees recognize. A logbook documents that someone arrived. Real security requires knowing who has arrived before, what they were doing, whether they have ever been refused entry at any block or gate, and whether their pattern of visits resembles anything the community should be paying attention to. None of that is possible in a system designed only to capture today’s traffic.
What Failure Looks Like in Practice
Three patterns repeat across both high-rise condominiums and landed gated communities, almost without exception.
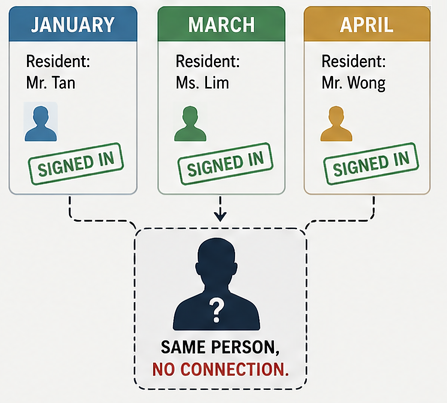
The first is the recurring stranger. A visitor enters under one resident’s name in January, another resident’s name in March, and a third in April. Each entry is correctly logged. None of the three hosts knows the others have hosted the same person. By the time a security incident occurs, the trail exists in fragments across separate logbook entries that nobody has reason to assemble. Manual logs cannot connect what they were never designed to connect.
The second is the silently lifted block. A visitor warned or banned after a previous incident arrives the next week and signs in without challenge. The ban exists in the chairman’s WhatsApp group, on a memo pinned in the guardhouse, perhaps in an email circulated to the management office. None of these are queried at the moment of entry, because the moment of entry is precisely when nobody has time to query them. A guard rotation, a different shift, or a different gate within the same development is all it takes to lift the block silently.

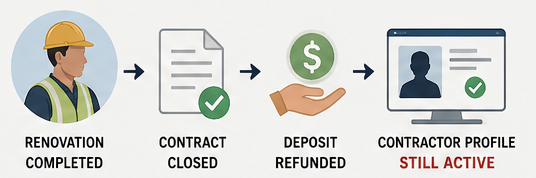
The third is the contractor who never left the system. A renovation contractor completes the job, the contract closes, and the deposit is refunded. The contractor’s details, however, remain valid in the visitor records, often retaining the same recognition pattern established during the renovation period. He returns six months later for what he describes as a brief follow-up. The guard, finding his profile listed, lets him through. He is no longer authorized, but the system has no concept of authorization expiring at the visitor level. The structural weakness here connects directly to how contractor access is provisioned in the first place, an issue covered in Managing Renovation Contractors in Residential Developments.
From Records to Profiles
The shift required is architectural, not procedural. A visitor record describes one event. A visitor profile describes a person. The difference may sound semantic, but it changes what security is structurally capable of doing.
A profile accumulates. Every visit the same person makes, regardless of which resident they visited, which guard processed them, or which gate they entered, attaches to a single identity. Visit count, visit pattern, host history, vehicles used, and any incidents involved all tie to that one profile. Over time the system knows the visitor better than any individual guard ever could.
A profile classifies. VIP, Regular, Frequent, Restricted, Consultant, Security Risk: these tags are not decorative. They change what happens at the gate. A Regular delivery rider arrives and the flow accelerates without the guard having to think about it. A Restricted profile arrives and the flow halts before any conversation begins.
A profile blocks at the source. Blocking can be applied at the level of face, identification number, or vehicle plate, which means the block follows the person across blocks, across gates, across vehicles, and across time. The visitor cannot edit himself back into the community simply by signing in under a different name or arriving in a different car.
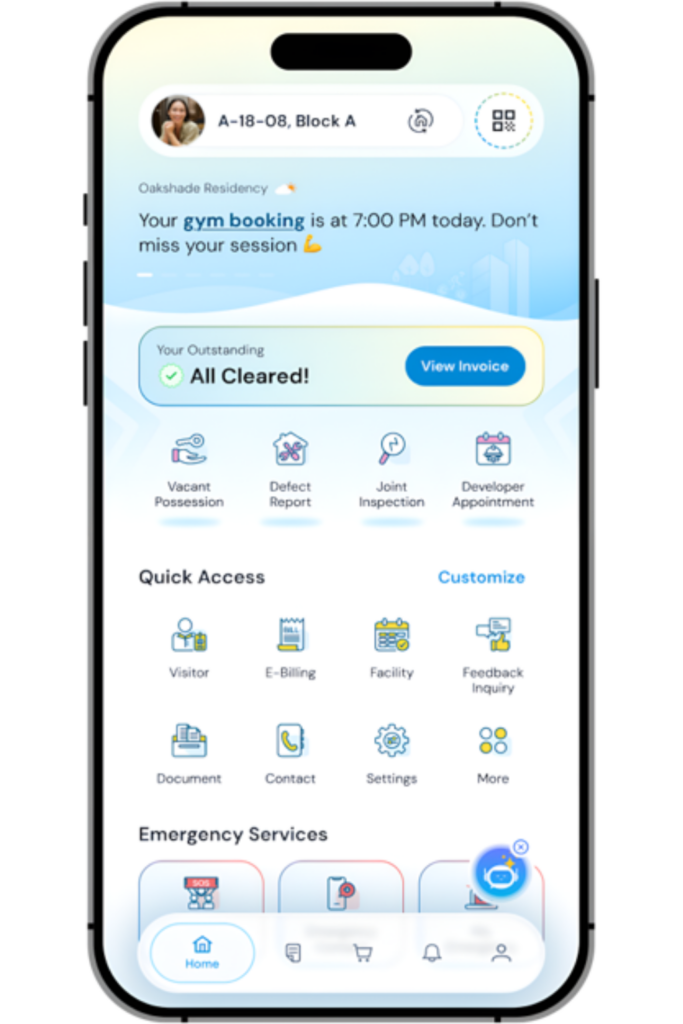
This is the architecture iNeighbour is built around in its current visitor management layer. Visitor profiles sit alongside the Flow Builder and live activity monitoring, so that when a guard processes someone at the iVizit guard app, the safety score, visit history, and any block flags appear on screen before access is granted. The decision is no longer made on the guard’s memory or the resident’s word. It is made on the community’s accumulated record.
Why This Matters for the Committee
JMB, MC, and RA committees carry the responsibility for community security. For strata properties governed under the Strata Management Act 2013, by-laws can govern access, restriction, and enforcement, but those by-laws are only enforceable if they can be applied consistently and at speed. Landed gated communities operate under their own house rules and residents association resolutions, which face the same enforcement test. A rule that bars a former tenant or a previously warned visitor from re-entering communal areas is a paper rule unless the system at the gate recognizes that person on sight. The profile is what makes the rule executable.
For management offices the benefit is operational. Fewer judgment calls at the gate. Fewer escalations to the chairman after the fact. Fewer late-night WhatsApp messages asking whether someone should have been let in. The system carries the institutional memory the guard rotation cannot.
A community that cannot remember its visitors cannot protect its residents.
